Networking Fundamentals (Udemy)
|Subscribers
Latest videos
Part 18 of Computer Networking Fundamentals: Building a Network
Part 17 of Computer Networking Fundamentals: Network Cable Types and Connectors
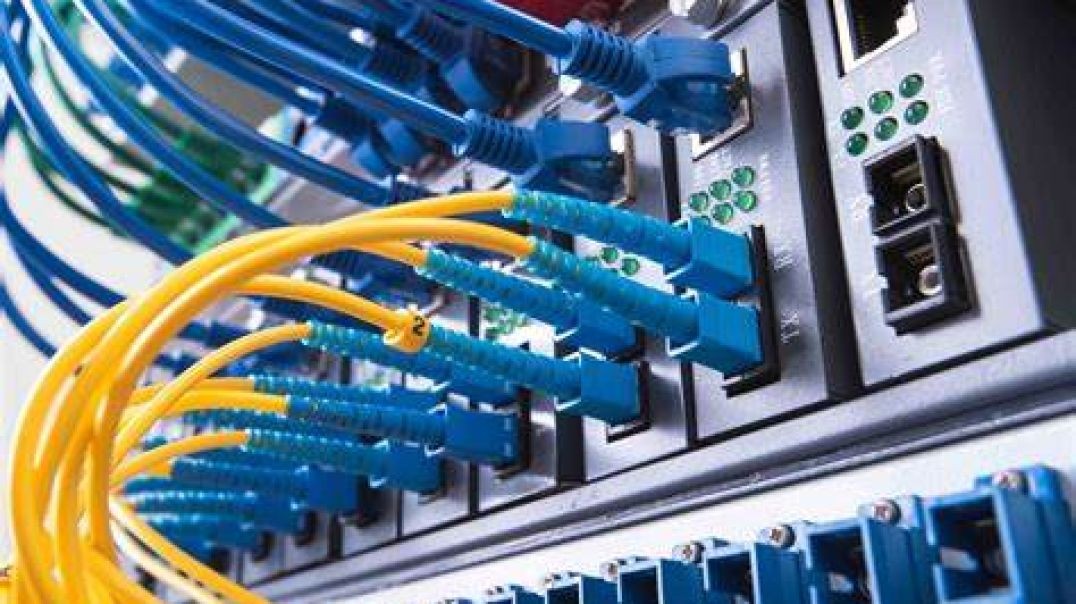
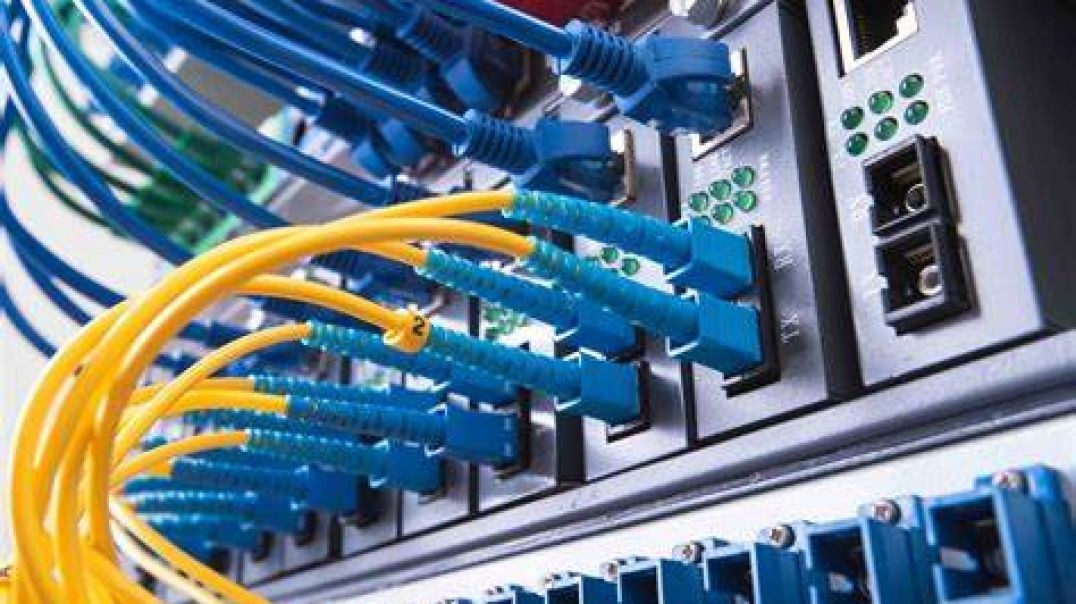
Cable Types and Connectors
At the end of this episode, I will be able to:
- Compare and contrast network cabling types, specifications and standards.
Learner Objective: Compare and contrast network cabling types, specifications and standards.
Description: In this episode, the learner will explore various network cable types, connectors and cabling standards.
- Introduction to Network Hardware
- Network Media Types
- Cable Types
- Copper - copper cabling is the most prevalent media in networks today. This type of media has a lower cost when compared to fiber
- Coaxial cabling - this type of copper media is mostly used in audio and video implementations today rather than networking. This cable type uses a centralized copper conductor wrapped in a dialectric coating, braided shielding and an insulating out jacket. The common connectors used for termination are BNC, F-type and T connectors.
- Twisted pair cabling - this is the most commonly used bounded network media in local area networks. This cable is comprised of 8 copper conductors, twisted in four pairs. These cable come in an unshielded variety called unshielded twisted pair or UTP as well as a shielded variety that wraps the internal conductors in a foil shielding called shielded twisted pair or STP. These cables use an RJ-45 connection for termination not to be confused with the smaller RJ-11 connector used in telephone systems.
- PVC grade cable - this twisted pair cabling is commonly used to connect computers to wall plates.
- Plenum grade cable - this cabling is used in premise wiring throughout plenum spacing for fire code.
- Fiber Optic - this type of cabling uses glass or plastic cores, cladding, strengthening fibers and an outer jacket. This network media has the fastest and farthest transmission distance of all bounded network media.
- Multimode fiber - this fiber optic cable uses cores of 50 and 62.5 microns and mulitple light sources to propagate the signal. It is the cheaper and shorter distance when compared to singlemode fiber.
- Singlemode fiber - this fiber optic cable uses a core of 9 microns and a single light source to propagate the signal. This type of fiber optic cabling is more expensive and farther transmission distances than multimode fiber.
- Connectors
- Subscriber Connector - An older square locking connector.
- Lucent connector - A smaller connector than the SC connector, providing a greater port density.
- Transceiver Modules
- SFP/SPF+ - these are modules are identical in size, however SFP support 1 Gbps transmission speeds and SFP+ supports 10Gbps.
- QSFP/QSFP+ - these modules are identical in size, the difference is that the QSFP support for four 1 Gbps links simultaneously and QSFP+ supports four 10 Gbps links simultaneously.
- Cable Categories - these are a set of specifications that were developed by the Telecommunication Industry Association/Electronics Industry Alliance or TIA/EIA as a part of the cabling standards endorsed by the American National Standards Institue (ANSI)
- CAT5e - this is the cable used in Gigabit Ethernet implementations capable of transmitting data a 350 Mbps
- CAT6 - this is the cable standards used in Gigabit Ethernet implementations capable of transmitting data at 1 Gbps
- CAT6a - this is the cable used in Gigabit Ethernet implementations capable of transmitting data up to 10 Gbps.
- Copper - copper cabling is the most prevalent media in networks today. This type of media has a lower cost when compared to fiber
- Ethernet Base Standards
- 10BASET = Ethernet implementation, 10 Mbps tranmission speed over twisted pair cables
- 100BASET = Fast Ethernet implementation, 100 Mbps tranmission speed over twisted pair cables
- 1000BaseTX = Gigabit Ethernet implementation, 1000 Mbps tranmission speed over twisted pair cables
- 10GBASELX - 10 Gigabit Ethernet implementation using fiber optic media.
- Cabling Issues
- Improper termination - internal conductors are crossed or damaged
- Electromagnetic interference - high voltage power sources, water fountains, HVAC systems, fluorescent lighting can cause interference and corrupt the communication signal in copper-based media.
- Damage - physical damage to the out jacket, internal conductors or cores can cause communication issues on the network
- Standards Mismatch - this can cause slower than expected or poor performance on the network or worse, no communications.
- Cable Types
- Network Media Types
Part 16 of Computer Networking Fundamentals: Routers
Routers
At the end of this episode, I will be able to:
- Describe the basics of routers and the routing process.
Learner Objective: Describe the basics of routers and the routing process.
Description: In this episode, the learner will identify the basics of routing and the routing process.
- Introduction to Network Hardware
- Routers+
- Routers - a connectivity device that determines the short path to send traffic. Routers can send traffic to networks that they are not connected to. Routers use IP addresses to determine where to send traffic and operates on layer 3 of the OSI model.
- Routing table - this routing element is a database that lists all the routes known to the router. These tables can be populated dynamically with a routing protocol or statically through manual configuration.
- Components
- Default route - is a route that routes traffic with no specific address of the next hop. In client computers this is typically the address of the default gateway.
- Network Destination - the network IDs of known destination networks.
- Netmask - the subnet mask for the destination network.
- Gateway - the IP address of the next hop to which the packet will be forwarded.
- Interface - this IP address or outgoing interface that connects to the destination network.
- Metric - a value assigned call a cost assigned to reach the destination network. The lower the cost, the better the route.
- Components
- Static vs. dynamic routing
- Static routing - these are manually defined routes that are configured by and admin. These routes will not change if a shorter route is learned by dynamic routing protocols.
- Dynamic routing - these are routes that are learning through routing protocols and communication with adjacent routers sharing routing information.
- Routing protocols
- Routing Information Protocol (RIP) - this is a dynamic routing protocol also known as a distance vector protocol that uses a hop count and the routing metric to determine the shortest path.
- Open Shortest Path First (OSPF) - this is a dynamic routing protocol also known as a link state routing protocol. OSPF is a complex routing protocol that uses the topology information of the nearest neighbor routers to determine the shortest path.
- Border Gateway Protocol (BGP) - this is a dynamic routing protocol used to determine the shortest path to route traffic across the Internet.
- The routing process
- When a router receives an IP packet, the router uses the destination IP address in the packet to determine where to send the packet. The router inspects it's routing table to identify the short path (route) to send the data.
- Network Address Translation (NAT) - this is a routing technique that allows network devices within a LAN area network, using private IP addresses, to send traffic across the Internet by translating private and public IP addresses.
- Routers+
Part 15 of Computer Networking Fundamentals: Network Switches
Switches
At the end of this episode, I will be able to:
- Identify the characteristics and basic functionality of a network switch.
Learner Objective: Identify the characteristics and basic functionality of a network switch.
Description: In this episode, the learner will be introduced to the basics of network switches, the basic is switching process and characteristics of a network switches.
- Introduction to Network Hardware
- Switches
- Managed vs. unmanaged
- Managed switch - this type of switch provides a configuration interface commonly in the form of a command line interface or terminal.
- Unmanaged - this is the most basic type of switch that requires no configuration tasks and utilizes a sort of "Plug and Play" implementation.
- Basic components
- Network adapter - this is a circuit board or embedded component installed on a network device such as a computer, smart tv, gaming console, VoIP phone and more. This component controls the communication for the network device.
- Network media - this is the bounded connection media that connects the network device to the switch. The most prevalent media is copper twisted pair cabling however fiber optic cabling is also used.
- Network Switch - this device receives the electrical communications from the network devices connected via ports on the face of the switch. These devices make decisions on what ports to forward the communications to.
- Media Access Control (MAC) address
- A MAC address is a unique 48-bit or 6-byte hardware identifier associated with a network adapter. This address is used to identify the network device on Ethernet switched networks.
- The MAC address is comprised of two components:
- 1st 3 bytes = Organizationally Unique Identifier (OUI) - a globally unique vendor/manufacturer identifier.
- 2nd 3 bytes = Unique LAN identifier - uniquely identifies the network adapter within the vendor/manufacturer.
- The switching process
- The switch receives a communication frame from a network device connected to one of the switch and adds the Media Access Control address of the network device to a database (MAC Table or CAM Table).
- The switch inspects the MAC Table for a device connected to a switch port with the matching destination MAC address in the received frame and forwards the data tothe appropriate network device.
- Switch Characteristics
- Port Speeds
- Ethernet = 10 Mbps (10Base)
- Fast Ethernet = 100 Mbps (100Base)
- Gigabit Ethernet = 1000 Mbps/1 Gbps (1000Base)
- Transmission Types
- Half Duplex - A link that can only communicate in a single direction at a time.
- Full Duplex - A link that performs simultaneous two-way communications
- Port Security
- DHCP Snooping - a technique that controls which ports are allowed to receive DHCP messages.
- ARP Inspection - a technique that rejects malicious ARP packets
- Flood Gaurd - a technique that prevents Denial-of-Service (DoS) attacks using malicious broadcast messages.
- VLANs
- Allows for the logical division or grouping of a subnet of the network devices connected to the switch.
- Port Speeds
- Physical vs. Virtual Switches
- Physical switch - a tangible hardware connectivity device.
- Virtual switch - a software-based application/element used in virtualization technologies.
- Layer 2 vs. Layer 3 switch
- Layer 2 - A switch that operates in the Data-link layer (L2) of the OSI model
- Layer 3 - A switch that is capable of using IP addresses, operating on the Network layer (L3) of the OSI model.
- Managed vs. unmanaged
- Switches
Part 14 of Computer Networking Fundamentals: Network Hardware
Network Hardware
At the end of this episode, I will be able to:
- Compare and contrast common network hardware.
Learner Objective: Compare and contrast common network hardware
Description: In this episode, the learner will be introduced to common network hardware.
- Introduction to Network Infrastructure
- Network Hardware
- Network adapters - a component that controls network communications for the device it is connect to or integrated into
- Repeaters/extenders - a network component that regenerates a signal, then re-transmits the signal to propagate the communications farther.
- Hubs - an older, largely obsolete network connectivity device that acts as a multi-port repeater. These network components do not make decisions on where to send the traffic and can reduce performance.
- Switches - a network connectivity device that forwards network communications between a series of ports. These devices rely on direct connections and use MAC addresses to determine where to send traffic.
- Routers - a network connectivity device that forwards traffic between networks based on IP addresses.
- Firewalls - a network component that is used to secure and control network traffic based on predetermined criteria.
- Voice Over IP (VoIP) phones - a network device can digitizes voice communications that can be routed across TCP/IP networks.
- Access points - a network connectivity device that allows wireless clients access to a wired network.
- Cable modems - a common network connectivity device used to provide Internet access using coaxial media.
- Dial-up modems - a network connectivity device that modulates and demodulates a digital signal, sent over analog PSTN (public switched telephone network) lines.
- Network Hardware
Part 13 of Computer Networking Fundamentals: Virtual Private Networks (VPN)
Virtual Private Networks
At the end of this episode, I will be able to:
- Identify and describe the characteristics and importance of VPNs.
Learner Objective: Identify and describe the characteristics and importance of VPNs
Description: In this episode, the learner will be introduced to virtual private networks or VPNs as well as the importance and attributes of this technology.
- Introduction to Network Infrastructure
- Virtual Private Networks
- A technology that allows for secure communications using public networks infrastructure
- Tunneling Protocols -
- Protocol - a set of rules for communications on a network
- Point-to-Point Tunneling Protocol (PPTP) - the oldest VPN tunneling protocol, while still in use, should be avoided due to vulnerabilities in the encryption and authentication.
- Layer 2 Tunneling Protocol (L2TP)- a combination of Microsoft's PPTP and Cisco's Layer 2 Forwarding (L2F), is a complex VPN protocol that is commonly coupled with IPSec for strong encryption.
- Microsoft Point-to-Point Encryption (MPPE)- an older encryption protocol used with dial-up connections and VPN technologies. This protocol is not considered to be secure and should be avoided where security is a concern.
- IP Security (IPSec)
- VPN Types
- Remote Access VPN - connects remote users to the organization's network from any location
- Site-to-site VPN - connects two local area networks together
- Virtual Private Networks
Part 12 of Computer Networking Fundamentals: Wireless Network Configuration
Wireless Network Configuration
At the end of this episode, I will be able to:
- Examine and implement a wireless network configuration.
Learner Objective: Examine and implement a wireless network configuration.
Description: In this episode, the learner will explore a demonstration of wireless network concepts through practical application of wireless network configuration.
- Introduction to Network Infrastructure
- Wireless network demo
- Components
- Wireless enabled laptop
- Ethernet cable (to connect to the access point)
- TP-Link TL-WA1201 AC1200 Wireless Access Point
- If necessary, perform factory reset on the AP
- Follow the procedures found on the vendor website
- Login to the AC point
- View the Status page
- Note - examine any current connections via the "Wired Clients" and "Wireless Client"* icons
- Click the "Quick Setup" tab
- Note* - Examine the options
- Access Point mode - the AP controls all communications on the network
- Range Extender mode - Relays signals to increase the transmission distance of the wireless network
- Client mode - acts as a networks adapter (or wireless client), allows other wired devices connect to the AP
- Multi-SSID mode - allows the Access point to create multiple wireless networks for VLANs and security.
- Note* - Examine the options
- Click the Network blade
- LAN - customize the IP address scheme for the AP and the LAN.
- DHCP Server - customize the DHCP server settings for the wireless network.
- Click the Wireless blade
- Wireless Settings - configure the SSID, encryption, mode, channel width and channel.
- Portal - creates a captive portal to direct clients to for authentication purposes
- WPS - enable or disable WPS
- Statistics - view the client's connection properties
- MAC Filtering - allow or deny access to the wireless networks based on the wireless client's MAC address
- Click the System Tools blade
- Time Settings, LED Control, SNMP, Ping Watchdog, Firmware upgrades, Backup & Restore, Reboot Schedule, Administration and Diagnostics
Part 11 of Computer Networking Fundamentals: Wireless Network Security
Wireless Network Security
At the end of this episode, I will be able to:
- Compare and contrast wireless security technologies.
Learner Objective: Compare and contrast wireless security technologies
Description: In this episode, the learner will explore a variety of wireless network security technologies.
- Introduction to Network Infrastructure
- Wireless Security
- WEP
- Weak or vulnerable to attack(Avoid)
- Uses a static key
- 64-bit or 128-bit key
- RC4 stream cipher
- CRC checksum
- WPA
- Weak or vulnerable to attack(Avoid)
- Uses Temporal Key Integrity Protocol
- Per-packet encryption
- RC4 stream cipher
- Message Integrity Check
- WPA2
- Stronger (Implement)
- Uses CCMP
- Counter Mode Cipher Block Chaining Message Authentication Code Protocol
- Advanced Encryption Standard
- 128-bit key
- WPA3
- Strongest
- Uses SAE
- 128-bit or 192-bit encryption
- WPS
- Push-button security
- Simplifies implementing security
- Weak or vulnerable to attack (Avoid)
- Disable
- Personal Mode
- WPA/WPA2/WPA3 implementation
- Requires no additional infrastructure
- Uses a preshared key or PSK (think password)
- Enterprise Mode
- WPA/WPA2/WPA3 implementation
- Requires additional infrastructure
- Utilizes 802.1X port-based authencation
- Requires a Remote Access Dial-in Server (RADIUS)
- MAC Filtering
- A security technique that identifies which wireless clients are allowed or denied access to the wireless network based on the client's media access control address.
- WEP
- Wireless Security
Part 10 of Computer Networking Fundamentals: Wireless Radio Frequencies
Wireless Radio Frequencies
At the end of this episode, I will be able to:
- Compare and contrast wireless frequencies used in wireless local area networks.
Learner Objective: Compare and contrast wireless frequencies used in wireless local area networks
Description: In this episode, the learner will identify the two frequency ranges used in wireless local area networks (WLAN).
- Introduction to Network Infrastructure
- Wireless Frequencies
- Industrial, Scientific and Medical (ISM) band
- 2.4 Ghz
- Channels
- 13 channels (11 available in the US)
- Each channel is 5 Mhz apart
- 22 MHz spacing is required between channels to reduce interference
- 3 non-overlapping channels (22 MHz spacing)
- Channel 1, channel 2, channel 3
- 802.11n allows for channel bonding
- 20 MHz and 40 Mhz
- Channels
- 2.4 Ghz
- Unlicensed Nation Information Infrastructure (U-NII) band
- 5 Ghz
- Channels
- 25 channels
- All channels are 20 Mhz wide and non-overlapping (unless bonded)
- The 5 GHz range allows for channel bonding
- 20 MHz, 40 MHz, 80 MHz and 160 MHz
- Channels
- 5 Ghz
- Industrial, Scientific and Medical (ISM) band
- Wireless Frequencies
Part 09 of Computer Networking Fundamentals: Wireless Standards
Wireless Standards
At the end of this episode, I will be able to:
- Compare and contrast wireless technology standards.
Learner Objective: Compare and contrast wireless technology standards.
Description: In this episode, the learner will be introduced to a variety of wireless specifications and standards.
- Introduction to Network Infrastructure
- Wireless networking
- Wireless Standards
- IEEE - Institute of Electrical and Electronics Engineers (IEEE)
- The world's largest association of technical professionals and standards body.
- Electrical, electronics, telecommunications, computer engineering
- 802 - is the standards committee that develops and maintains networking
- Wi-Fi Alliance - a non-profit organization that owns the Wi-Fi trademark. Manufacturers may use the trademark to brand products certified for Wi-Fi interoperability. standards for LANs, MAN, and their wireless counterparts WLAN, WPAN, WMAN as well as Ethernet and bridging technologies.
- 802.11 - is the standards committee for wireless LAN RF communication standards
- 802.11a - (1999)released along side .11b, 5 GHz frequency @54Mbps
- 802.11b - (1999)released along side .11a, 2.4 GHz frequency @11Mbps
- 802.11g (Wi-Fi 3)- (2003)2.4 GHz @54Mbps, supports backward compatibility with .11b devices
- 802.11n (Wi-Fi 4) - (2009) 2.4 GHz and 5 GHz, @600Mbps, supports backward compatibility with all earlier 802.11 standards, increased channel width.
- 802.11ac (Wi-Fi 5) - (2014) 5 GHz, @1.3 Gbps-2.3 Gbps
- 802.11ax (Wi-Fi 6/6E) - (2021) 2.4 GHz,5 GHz and 6 GHz, @9.6 Gbps
- IEEE - Institute of Electrical and Electronics Engineers (IEEE)
- Bluetooth
- Wireless communication technology operating in the 2.4 GHz ISM band
- Bluetooth 1.* (1999)- 732 Kbps (10m or 32.8 ft)
- Bluetooth 2.* - (2004) (Enhanced Data Rate or EDR) 3 Mbps (10m or 32.8 ft)
- Bluetooth 3.0 - (2009) (+ High Speed or +HS) (up to 24 Mbps over Wi-Fi) (10m or 32.8 ft) excessive power consumption
- Bluetooth 4.* - (2010) (Bluetooth Low Energy or BLE) 1 Mbps (610m or 32.8 ft)
- Bluetooth 5.* (2016)- 2 Mbps (10m or 32.8 ft)
- Infrared
- Short-range line-of-sight communication
- Specifications are controlled by the Infrared Data Association (IrDA)
- Standards
- Serial IrDA (SIR) - 115.2 Kbps
- Fast IrDA (FIR) - 4 Mbps
- Very Fast IrDA (VFIR) - 16 Mbps
- Wireless Standards
- Wireless networking
Part 08 of Computer Networking Fundamentals: Network Topologies
Network Topology
At the end of this episode, I will be able to:
- Compare and contrast network topologies.
Learner Objective: Compare and contrast network topologies.
Description: In this episode, the learner will explore different network topologies such as bus, ring, star, mesh and hybrid network topologies.
- Introduction to Network Infrastructure
- Network Topology - This defines the arrangement of network elements such as nodes, connectivity devices, connections and how these relate to one another as well as the flow of the data. There are two way to depict topologies, physical and logical.
- Physical topology - describes the tangible arrangement and aspects of the network elements.
- Logical topology - describes the flow of the data across a network's elements.
- Types
- Bus - a topology in which all devices on the network are connected to a central network media (bus) such as coaxial cabling. This type of topology has been phased out due to performance and scalability issues.
- Ring - a topology in which all devices are connected to a network media with and upstream and downstream "neighbor" forming a circle. In LAN-based communications, ring-based topologies have been phased out (Token Ring, Fiber Distributed Data Interface or FDDI), however in WAN-based technologies they are still used (SONET).
- Star - a common topology in modern networks in which all devices are connected to a centralized device forming a star pattern.
- Mesh - a complex network topology in which all devices have multiple connections to every other device. This topology is very resilient to connection failures.
- Hybrid - a topology that combines characteristics of more than one of the other topologies.
- Network Topology - This defines the arrangement of network elements such as nodes, connectivity devices, connections and how these relate to one another as well as the flow of the data. There are two way to depict topologies, physical and logical.
Part 07 of Computer Networking Fundamentals: Additional Network Types
Additional Network Types
At the end of this episode, I will be able to:
- Compare and contrast network types.
Learner Objective: Compare and contrast network types.
Description: In this episode, the learner will explore additional network types such as personal area networks (PAN), metropolitan area networks (MAN), campus area networks (CAN) and storage area networks (SAN).
- Introduction to Network Infrastructure
- Additional Network Types
- Personal Area Networks (PAN) - A network that is typically an individual's or user's immediate vicinity. The range is common a meter to 10 meters. Common devices are Wi-Fi and Bluetooth peripherals
- Metropolitan Area Network (MAN) - A network that spans a larger geographical area than a local area network, but a smaller coverage area than a wide area network. The coverage area is a single city, municipality or in some instances multiple cities.
- Wireless Metropolitan Area Network (WMAN) - A network in which the scope is the same as a traditional met area network, using unbounded media such as the Wireless Interoperability for Microwave Access or WiMAX.
- Campus Area Network (CAN) - A network that is very similar to the scope of a metropolitan area network, however is under the control of a single academic body.
- Wireless Wide Area Networks (WWAN) - A network that is the same in coverage area to a traditional wide area network, using cellular communications such as 3G, 4G, 5G and LTE to communicate.
- Storage Area Networks (SAN) - a network type that utilizes high-speed connections, using Fiber Channel, interconnected switches, fiber optic media, connecting servers to data storage.
- Additional Network Types
Part 06 of Computer Networking Fundamentals: Wide Area Networks (WANs)
Wide Area Networks
At the end of this episode, I will be able to:
- Describe the components and attributes of a wide area network.
Learner Objective: Describe the components and attributes of a wide area network
Description: In this episode the learner will identify the components and attributes of a wide area network.
Introduction to Network Infrastructure
- Wide area networks (WAN)
- What is a wide area network? - A network that groups together or connects more than one local area networks. These networks utilized a combination or short-range private network links as well as long range carrier provided public links.
- Connection Types
- Leased Lines
- Direct Connections (On-premise to cloud)
- Channelized Carrier Standards
- T1 = 1.55 Mbps
- T3 = 44.736 Mbps
- OC1 = 51.84 Mbps
- OC3 = 155.52 Mbps
- Multiprotocol Label-Switching (MPLS) - this is a WAN technology that uses labels to determine the shortest path, instead of network addresses. The multiprotocol label switching technology is implemented in a mesh topology.
- Synchronous Optical Networking (SONET) - this is a WAN technology that can transmit large amounts of data over long distances using fiber optic media. The SONET technology implements a fault-tolerant ring topology.
- Digital Subscriber Line (DSL) - this is WAN technology allows digital data and voice signals to be transmitted over traditional telephone networks call public switched telephone network or PSTN copper media. The most common DSL type is called asymmetrical DSL or ADSL, providing faster downloads than uploads
- Dialup - this is one of the oldest networking technologies using copper media with data being transmitted over public switched telephone networks or PSTN. Dialup is a digital signal that is modulated over a analog carrier via a modem.
- Leased Lines
- Wide area networks (WAN)
Part 05 of Computer Networking Fundamentals: Demarcs and Perimeter Networks
Demarcation and Perimeter Networks
At the end of this episode, I will be able to:
- Describe the characteristics and importance of demarcation points and perimeter networks.
Learner Objective: Describe the characteristics and importance of demarcation points and perimeter networks.
Description: In this episode, the learner will explore what demarcation points and perimeter networks are as well as what the importance of these technologies are in networking.
- Introduction to Network Infrastructure
- Demarcation point - The physical point that a carrier's network connection ends and a private network starts (think network boundaries). The term demarcation is often abbreviated demarc.
- Types of demarcation points
- Residential - These are utilized in homes, either at the first socket (typically the kitchen) or a junction box on the exterior of the house
- Business - These demarcation points are either installed on the exterior of the building, or the carrier will install a specialized device within the interior of the building at a main distribution frame (think server closet/datacenter)
- Demarcation wiring runs either overhead or underground
- A demarc is important to understand in networks today as this marks the point of responsibility for networked components and service. The carrier's network up to the demarc is the responsibility of the carrier, however the demarc point that connect on the residential or business side is the responsibility of the subscriber.
- Demarc connections can be fiber, coaxial or PSTN lines
- Types of demarcation points
- Perimeter Network (Screened Subnets) - A logical boundary between a privately owned network and the Internet. There are other names for perimeter networks such as demilitarized zone (DMZ), screened subnet and edge network.
- Purpose
- Security - A companies internal network must remain secure and not allow public access. Most organizations will install security devices in the perimeter network to control the flow of inbound and outbound traffic such as firewalls, intrusion detection systems (IDSs), intrusion prevention systems, honeypots or devices called unified threat management systems (UTM) which combine all the previous devices' functionality into one centralized device.
- Purpose
- Demarcation point - The physical point that a carrier's network connection ends and a private network starts (think network boundaries). The term demarcation is often abbreviated demarc.
Part 04 of Computer Networking Fundamentals: Wired Local Area Networks vs. Wireless Local Area Networks
Wired LANs vs Wireless LANs
At the end of this episode, I will be able to:
- Compare and contrast wired and wireless LAN implementations.
Learner Objective: Identify the characteristics and importance of VLANs
Description: In this episode, the learner will be introduced to the basic constructs and characteristics of wired and wireless local area networks.
- Introduction to Network Infrastructure
- Wired LAN
- Devices in this type of LAN are connected using bounded media
- Bounded media types
- Copper - The most prevalent LAN-based network medium used today. This medium uses single or multiple copper conductors to transmited data.
- Fiber - These medium uses an optical light source to transmit data through a concentrated core made of either plastic or glass.
- For devices to communicate, they need to be physically connected via Ethernet switch
- Due to the nature of the physical connections, wired networks can provide a higher level of security than wireless networks
- Wired LANs can have constraints
- Limitation of cabling (distance, electromagnetic interference, damage)
- Building requirements (historical sites, cumbersome installations, proximity to the connectivity device)
- Mobility is challenging
- Wireless LAN
- Devices in this type of LAN connect to the network via radiated energy
- Wireless LAN Types
- Infrastructure mode - In this type of Wireless LAN, a centralized network device called a wireless access point controls all communications on the network.
- Ad-hoc mode - In this type of Wireless LAN there is no centralized connectivity device. The wireless devices communicate directly with each other.
- Wireless LANs have become increasingly more popular due today because:
- Ease of installation
- Reduction of physical cabling
- Mobility
- Simplicity to add devices to network
- Disadvantages
- Communication eminations
- Obstacles and interference
- Network saturation and congestion
- Hybrid LAN
- Most common LAN deployment in modern networks today
- This type of LAN combines both wired and wireless communication
- Wired LAN
- Workstations and servers (these are stationary devices)
- Wireless LAN
- Laptops, tablets, smartphones (these are devices that require mobility)
- Any stationary device that requires a connection, but cabling is not feasible or possible
- Wired LAN
Part 03 of Computer Networking Fundamentals: Virtual Local Area Networks (VLANs)
Virtual Local Area Networks
At the end of this episode, I will be able to:
- Identify the characteristics and importance of VLANs.
Learner Objective: Identify the characteristics and importance of VLANs
Description: In this episode, the learner will be introduced to Virtual Local Area Networks or VLANs as well as identify the purpose of implementing them in networks.
- Introduction to Network Infrastructure
- What are VLANs? - A logical division of networked devices connected within a local area networked
- Why are VLANs important? - VLANs allow administrators to divide ports on a switch into logical groupings. This creates multiple logical switches out of a single physical switch. This can be done for performance and security.
- Understanding communication types
- Broadcast - A communication message that is sent by a single device to every other device connected to the switch.
- One to all communication
- Unicast - A communication message that is sent by a single device to another device on the network.
- One to one communication
- Multicast - A communication message that is sent by a single device to a group or subset of the devices on the network.
- Broadcast domain - A group of devices connected to a network that receive broadcast communications. This grouping can be based on physical or logical segments.
- Segments - A divison that splits a network into smaller parts.
- Broadcast - A communication message that is sent by a single device to every other device connected to the switch.
- Performance benefits - VLANs create virtual boundaries that reduce the amount of broadcast traffic between devices on a larger network and ease administration.
- Security benefits - VLANs allow network administrators to group devices together to assign an enforce security policies. Devices within a VLAN can only communicate with other devices assigned to the same VLAN.
- How are VLANs implemented?
- VLANs require configuration of managed switches.
- VLANs use tagging information that is inspected by the switch to determine which VLAN the communication belongs to.
Part 02 of Computer Networking Fundamentals: Local Area Networks
Local Area Networks
At the end of this episode, I will be able to:
- Describe the components and attributes of a local area network.
Learner Objective: Describe the components and attributes of a local area network
Description: In this episode, the learner will identify the components and attributes of a local area network.
- Introduction to Network Infrastructure
- Local area networks (LAN)
- What is a network? - A group of computers, connected to common network links for the purpose of communication and sharing resources.
- What are LANs? - A network comprising a single geographical region.
- Components
- Client workstations
- Laptops
- Mobile devices
- Servers
- Cabling - bounded transmission media
- Standardized media
- Copper or fiber
- Connectivity or intermediate devices (Access points, switches, routers)
- Network Models
- Host-based - a centralized powerful computer performs all storage and processing of data. User inputs are captured from terminals, output is displayed on the terminal.
- Client/Server - The most popular network model in modern networks, in which computers called clients request services and resources from other computers. Servers are the computers in a client/server network that respond to and provide services based on client requests.
- Peer-to-peer - a decentralized network model in which every device evenly (peer) shares the various functions of the network (requesting resources and providing resources).
- Local area networks (LAN)
Part 01 of Computer Networking Fundamentals: Overview